Disclaimer: this gained knowledge, application and post was made possible by COVID-19 lock down, there is something positive in everything.
Things covered are as below, you may head to below items specific to your needs if required:
-
Raspberry PI Headless, WIFI and SSH enabled (We want the PI to use only the resources required and also be in position to handle a load of multiple services running on same PI)
-
DDNS such as No-IP (Use this if you can Port Forward on LAN, as it will update your current IP to a dynamic domain name, this may not be secure as port forward and dynamic domain is fixed and connected directly to your home / personal network but its faster*)
-
Ad Blocker, Internet Tracker / Filter and DNS using Pi-Hole (This will save up data as your network will block ads and also save you on ad disruptions on your devices and give you more control on blocking / allowing sites)
-
VPN using WireGuard UDP only, else OpenVPN if you might need TCP (As most most Proxy Server might not support UDP)
-
Port Forward (not secure but faster*)
-
Reverse Tunnel (If you do not want / can not / using mobile data / port forward is not possible / or simply make your pi portable / accessible regardless on which network you are on)
* means it will be elaborated later on, the steps will be bundled up based on the required steps / stages in setup / heading herein, I will divide the steps based on port forwarding or not in the stage in setup / heading such as:
-
If you will be port forwarding then setup DDNS such as No-IP and Forward the Port from Router to Raspberry Pi
-
If you will not be port forwarding skip the above option and just setup Reverse Proxy such as RemoteIT with the rest of the setup
So being on the move I tend to use the internet a lot, understanding and knowing the ins and outs of free WIFI I tend to use my Mobile network instead, which means more data bills, and having a free VPN are mostly running on quota or the hassle of not being able to access anything from home while on the go limit on device, 2 problems to be solved:
-
Use of Free WIFI Securely without VPN Payment or limited quota / device connected
-
Access home network / devices / files securely on the go
The first time I heard of “raspberry pi / raspberry pie” I thought it was something I could eat ![]() , apparently it is the number π is a mathematical constant and there is a “PI Day” that is annually celebrated and observed on March 14 (3/14 in the month / day format).
, apparently it is the number π is a mathematical constant and there is a “PI Day” that is annually celebrated and observed on March 14 (3/14 in the month / day format).
So after one week of research and review, I was going for Pi Zero but on the second week knowing how I would probably get excited, I went with the highest specs available for any over kill I had in mind, as the post title suggests that’s a mouth full already and while the initial intention was VPN only and just to solve two things, I ended up with more due to the benefits and restrictions faced during setup (Blocked by ISP).
-
Raspberry Pi Zero W 1GHz, single-core CPU / 512MB RAM
-
Raspberry Pi 4 B Broadcom BCM2711, Quad core Cortex-A72 (ARM v8) 64-bit SoC @ 1.5GHz / 4GB LPDDR4-3200 SDRAM
For this setup you will need a casing for protection, heat sinks and fan/s to keep cool the raspberry pi.
Word of advice always go to the source for anything, unless not available then only look somewhere else, as most of them are outdated, I have personally researched and compared from different sources including YouTube video tutorials, below I will lay down the process and procedure, including links within from OEM providers to the Software providers, first thing first.
1. Raspberry Pi Installation / Setup
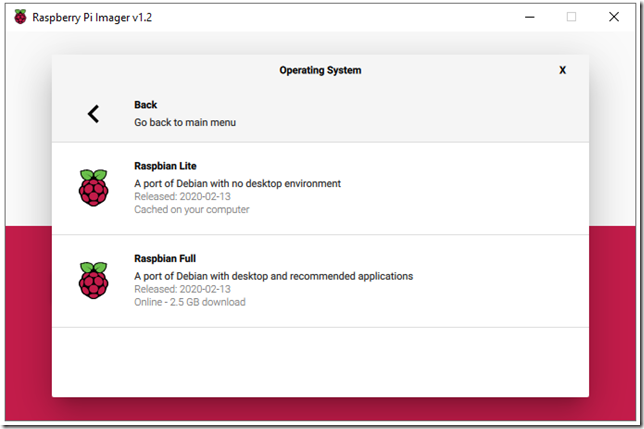
Most tutorials talks about downloading the OS Image and then write it to the SD Card, this is fine if you want to do it multiple times or have limited data, the best and recommended way is to use Raspberry Pi Imager as it will allow you to choose one of the multiple supported OS, set proper file format i.e fat32 and write it directly into your selected SD straight away.
I chose headless setup for this instance meaning I will not be using a monitor and hence there is no need to install the desktop software. I used “Raspbian Lite” on 8GB SD Card for my setup. I also did install “Raspbian Full” on 16GB SD Card separately when I need to have extra desktop I just swap the SD cards and plugin HDMI, Keyboard and Mouse, bear in mind SD Cards larger than 32GB have a further read on sdxc formatting.
Also do take note, pi-hole will have its own database meaning there will also be a lot of write to SD Card, so ensure the card can handle it such as class 10 and above, not only the SD Card Size matters but also it’s Read/Write Speed.
Go to “Raspbian (Other)” to get option for “Raspbian Lite”.
2. Enable SSH and WIFI Connection
We will need to create 2 files named exactly as specified:
-
wpa_supplicant.conf (Specify 3 things country code, network name and password)
-
ssh (Empty)
Example: Malaysia = MY
ctrl_interface=DIR=/var/run/wpa_supplicant GROUP=netdev update_config=1 country=MY network={ ssid="MyWifiName" psk="MyWifiPassword" }
Now we have those 2 files saved in the SD Card, remove the SD Card from you desktop and insert it into the raspberry pi, switch on the power and you should see 2 led light up, red for power, green blinking for reading data (the blink will end once reading / boot complete), you could give it 10 seconds but less than 5 being headless its already up and running.
3. Connecting to your Raspberry PI
You could open up your router to see new local IP address connected, as most tutorial specify SSH using local IP address or Putty for windows for SSH, you do not need that.
You will need specific IP address if you have multiple PI on Network and for Windows 10 you do not need Putty, for my case having SSH already on my Windows 10 as I am using AWS and Git, I just open up CMD as below:
| >ssh raspberrypi.local -l pi |
The command allows us to “-l” login user named “pi” directly after this we just enter the default password “raspberry”.
4. Change Pi Password and Update packages
After connecting to your PI it is best to change password as I intend the device to be wireless, headless and portable, meaning I could run it in another network, hence password change is a must, run below and press enter, follow the on screen prompt for current and new password.
| >passwd |
Update your raspberry pi, most tutorials will simply use apt-get to update and upgrade but the Debian base Linux commands have been simplified so simply trigger below and enter.
| >sudo apt update |
| >sudo apt full-upgrade |
“full-upgrade” is used in preference to “upgrade”, as it will also include any dependencies that may have been made changed / updated for a specific package.
Make it a habit to reboot so some of the update that require reboot to take effect, on every step / after update / installation, so do trigger reboot then SSH back.
| >sudo reboot |
Also make it a habit of shutting down your raspberry pi properly rather than following the online tutorials which suggest switching off the main plug or removing the plug, this will lead to corrupt data and even ruin your SD Card as it could be in write mode when power is lost.
This will shut it down within 60 seconds:
| >sudo shutdown |
To halt and shutdown immediately use:
| >sudo shutdown -h now |
5. DDNS No-IP (Only setup if you intend to port forward)
How to know if you can port forward if you want to?
-
Data / Internet Provider gives you a static IP address / it is a land line / not SIM, mobile operators control NAT, users might be on a shared public IPs. You wont be able to forward it as you do not control the gateway / server. (Such as my case on Celcom)
-
You Own and have access to the router, if you are in the first router you will need to port forward once else based on the network topology you will need to forward up to your PI
Here are the steps directly from the source:
-
>mkdir /home/pi/noip
-
>cd /home/pi/noip
-
>tar vzxf noip-duc-linux.tar.gz
-
>cd noip-2.1.9-1
-
>sudo make
-
>sudo make install
-
>sudo /usr/local/bin/noip2
-
>sudo noip2 -S
Remember port forwarding opens up port into your network, which means your network might be susceptible to attacks, and on top of that DDNS it will have a fixed domain name to your network, meaning you just need to know it once for yourself and the attacker, and won’t be portable in the event you take it somewhere you will need to port forward from the new router.
This set up will be faster in a sense you will be connected directly to your network without using reverse proxy and you have more control of your own data and network settings as a whole.
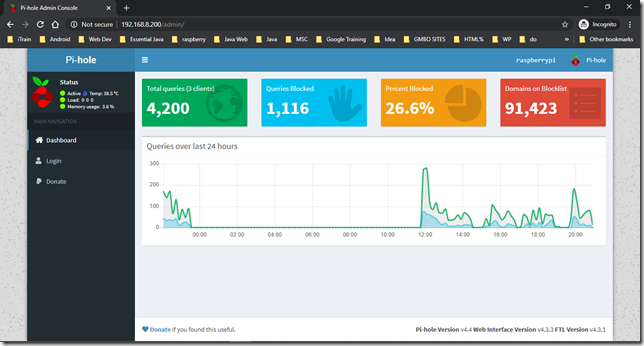
6. Ad Blocker, Internet Tracker / Filter and DNS using Pi-Hole
It is best to have a combo of both PiVPN and Pi-hole running in the network but the setup issues is that most of the tutorials installs PiVPN (OpenVPN / WireGuard) first followed by Pi-hole which leads to re-setting / re-configure of DNS.
If you intend to install both then its best to install Pi-Hole first as when it comes to installing PiVPN, existing Pi-Hole will be detected and the installation script will ask if you want to use it as the DNS for the VPN, follow below:
| >curl -sSL https://install.pi-hole.net | bash |
Follow on Screen steps, basically you will need to have:
-
Static IP (Manually set on the device) / DHCP Static Binding (Set on Router which most modern routers already have it)
-
Enable ip4 and ip6 (Already default selected)
Everything else can be left as default including installing the pi-hole web and server, unless you have specific needs, at the end of the script you will be presented with a login password for Pi-Hole on Screen (you may simply screen shot) and also on terminal (you may simply copy).
At this point you may set up your router to point to Pi as your DNS server as in my case this is not possible else specific devices, you might also notice ip6 “not configured” even though you selected it, you might login as admin and fix it.
7. Virtual Private Network using PiVPN (OpenVPN / WireGuard)
This Pi VPN setup also uses a script with option run below and follow the prompt:
| >curl -L https://install.pivpn.io | bash |
I am doing Port Forwarding:
-
Select DDNS instead of Static IP Address and input your domain / provided sub-domain
-
Select either OpenVPN / Wire Guard but UDP
I am not doing Port Forwarding:
-
Select Static IP Address (DHCP Reserve or Static IP)
-
Select OpenVPN TCP (Default will be 443) setup to port 1194 (Some proxy servers have scripts for specific usage or ports for setup hence default will work best / Known protocal)
Everything else should be default unless you want to have random ports for security or changing other settings you may see fit, after installation you will need to add users, add users based on how many will access the VPN, it is best to add users based on the number of devices that will need to connect, as there can not be simultaneous connection of an account / user.
With user password
| >pivpn add |
Without user password
| >pivpn add nopass |
8. Port Forwarding
This option is for those who fall under “I am port forwarding”, simply forward the PiVPN port you selected during setup if it is OpenVPN or WireGuard both will be UDP, depending on specific router, you may find instructions of your router.
There is no need to forward multiple ports i.e port 80 for pi-hole web, 22 for SSH, just forward “One port to rule them all” and that is your VPN port as it will create a tunnel into you network and you will virtually be in the same topology / network and you can access them securely as being in a LAN over WAN.
9. Reverse Proxy / Tunnel using Ngrok / RemoteIT
This option is for those who fall under “I am not port forwarding”, to access your raspberry pi in your network or any other network or if your ISP blocks ports, you will need to set up VPS or in our case a proxy to be specific “Reverse proxy” where communication will take place there.
This is rather secure manner of communication and given some providers randomly generate end points and port mapping to your original values for each connection, it becomes hard to be attacked as those values become useless after disconnection and also options of only allowing one active connection per service which ensure its only you active accessing your resources at that point and time.
You may proceed to setup a VPS as a Reverse Proxy Server or use existing one, there are many more, its up to you to compare and choose, example such as:
-
> unzip /path/to/ngrok.zip
-
>./ngrok authtoken ZMD3UjmSs2LEWmonFxP234453qdTYDgUmrAUBgomNu6Hi (Swap with your authorization token)
-
> ./ngrok http 80 (Swap the service and port number)
-
>sudo apt update && sudo apt install -y connectd && sudo connectd_installer
Follow the on Screen Prompt, select option 1 for an application running on Pi
Then select option 9 you for OpenVPN you may leave the port as default as specified in this guide else specify the port you provided.
Validate registered device
Some routers may have inbound and outbound rules, in my case the inbound rules can not be changed but the outbound rules are available, which allow application such as online games, video conferencing, or IP phone over the LAN to take place, these can be found in router setting > security outbound rule / > special applications
To escape this set up you could easily attach the port to a known service that either major OS or the router it self uses, these are open most of the time so as to not restrict services either 22 (SSH) or 443 (HTTPS) as explained on Hide OpenVPN Traffic.
10. Connection
Now remember that pivpn command you used to add user / device? We may extract that from Pi, we could simply use SFTP, my favorite right out of notepad++ just add a plugin, right click the created file and select “Download File”.
Now time to connect from remote, you will need to generate the proxy values:
-
Proxy End Point / URL
-
Proxy Port
You can do this from the web portal of your reverse proxy provider / server, grab those two values and swap them from the .ovpn file and connect, lets test by leaving my network and connect to another network.
Now that I am connected to another network lets start OpenVPN.
Success you can see data transfer started and I am able to access everything in my home network through the VPN as if I was in LAN.
Things setup / Achieved
-
Headless Raspberry Pi with SSH and WIFI
-
Ad Blocker + Traffic Tracker / Filter + DNS using Pi-hole
-
VPN using PiVPN
-
Reverse Proxy using RemoteIT
-
No unnecessary DDNS Service
-
No Opening Ports / Port Forward in my network
-
Truly portable box, I just connect to new WIFI
With the above setup I just need the power cable to enjoy all the services, it also means I could carry it around remember portability and use Pi-hole on the go without VPN or leave it in another network and access it remotely using RemoteIT, surely “petite and portable” ![]() .
.
Conclusion
Due to DIY nature of Raspberry PI, I think it would be great to have:
-
Power on / off toggle switch, so it would gracefully shutdown by halting all services prior killing the power
-
Temperature triggered fan rather than having it on with power on
These can be achieved by python scripts using the GPIO pins, then it would be with a breeze without SSH into it to trigger shutdown and power efficient with a temperature triggered fan.














Hi! I work for remote.it in USA. Thank you for mentioning our system in your excellent blog post! Would love to chat with you about VPN applications. I need some help with OpenVPN on pi. I can show you how to use remote.it without a proxy relay server too for best performance. To address your correct concern about reverse proxy vs. port forwarding performance. Hope to hear from you!
Hi, yes peer to peer will counter the performance issue addressed, I have also looked into the released remote it pi that allows this to happen, I will add herein for future users:
– https://www.youtube.com/watch?v=uqS22oQDwfg&feature=youtu.be
– https://www.youtube.com/watch?v=j9EsCvBF-cA&feature=youtu.be
Thank you and stay safe.
thanks for your blog post! will this solution also work to use the pi-hole capabilities remotely, specifically mobile devices on mobile data? Thanks!
Yes that exactly the point in this blog post:
“mobile operators control NAT, users might be on a shared public IPs. You wont be able to forward it as you do not control the gateway / server. (Such as my case on Celcom)”
you will need to follow instructions on:
9. Reverse Proxy / Tunnel using Ngrok / RemoteIT
Cheers.
pivpn in “not detected” status on remote.it. kindly help please?